312-50v11 | The Secret Of EC-Council 312-50v11 Questions Pool
Our pass rate is high to 98.9% and the similarity percentage between our 312-50v11 study guide and real exam is 90% based on our seven-year educating experience. Do you want achievements in the EC-Council 312-50v11 exam in just one try? I am currently studying for the EC-Council 312-50v11 exam. Latest EC-Council 312-50v11 Test exam practice questions and answers, Try EC-Council 312-50v11 Brain Dumps First.
Online EC-Council 312-50v11 free dumps demo Below:
NEW QUESTION 1
The tools which receive event logs from servers, network equipment, and applications, and perform analysis and correlation on those logs, and can generate alarms for security relevant issues, are known as what?
- A. network Sniffer
- B. Vulnerability Scanner
- C. Intrusion prevention Server
- D. Security incident and event Monitoring
Answer: D
NEW QUESTION 2
ViruXine.W32 virus hides their presence by changing the underlying executable code.
This Virus code mutates while keeping the original algorithm intact, the code changes itself each time it runs, but the function of the code (its semantics) will not change at all.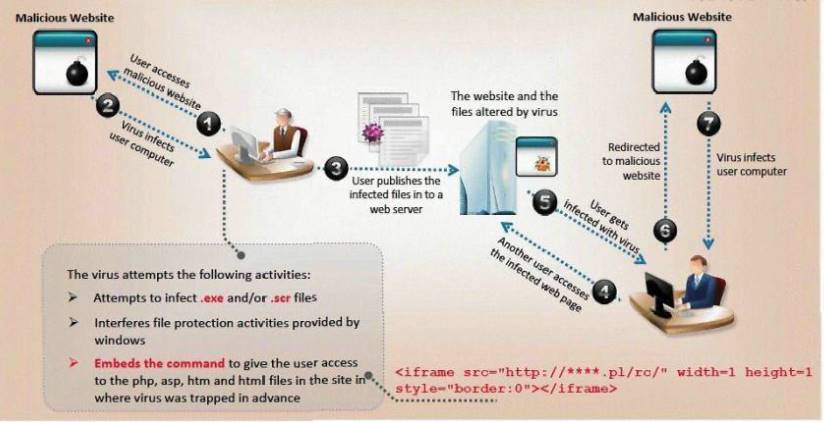
Here is a section of the Virus code:
What is this technique called?
- A. Polymorphic Virus
- B. Metamorphic Virus
- C. Dravidic Virus
- D. Stealth Virus
Answer: A
NEW QUESTION 3
The network administrator at Spears Technology, Inc has configured the default gateway Cisco router's access-list as below:
You are hired to conduct security testing on their network.
You successfully brute-force the SNMP community string using a SNMP crack tool.
The access-list configured at the router prevents you from establishing a successful connection. You want to retrieve the Cisco configuration from the router. How would you proceed?
- A. Use the Cisco's TFTP default password to connect and download the configuration file
- B. Run a network sniffer and capture the returned traffic with the configuration file from the router
- C. Run Generic Routing Encapsulation (GRE) tunneling protocol from your computer to the router masking your IP address
- D. Send a customized SNMP set request with a spoofed source IP address in the range -192.168.1.0
Answer: BD
NEW QUESTION 4
Within the context of Computer Security, which of the following statements describes Social Engineering best?
- A. Social Engineering is the act of publicly disclosing information
- B. Social Engineering is the means put in place by human resource to perform time accounting
- C. Social Engineering is the act of getting needed information from a person rather than breaking into a system
- D. Social Engineering is a training program within sociology studies
Answer: C
NEW QUESTION 5
Which of the following is the primary objective of a rootkit?
- A. It opens a port to provide an unauthorized service
- B. It creates a buffer overflow
- C. It replaces legitimate programs
- D. It provides an undocumented opening in a program
Answer: C
NEW QUESTION 6
Hackers often raise the trust level of a phishing message by modeling the email to look similar to the internal email used by the target company. This includes using logos, formatting, and names of the target company. The phishing message will often use the name of the company CEO, President, or Managers. The time a hacker spends performing research to locate this information about a company is known as?
- A. Exploration
- B. Investigation
- C. Reconnaissance
- D. Enumeration
Answer: C
NEW QUESTION 7
The following is an entry captured by a network IDS. You are assigned the task of analyzing this entry. You notice the value 0x90, which is the most common NOOP instruction for the Intel processor. You figure that the attacker is attempting a buffer overflow attack.
You also notice "/bin/sh" in the ASCII part of the output. As an analyst what would you conclude about the attack?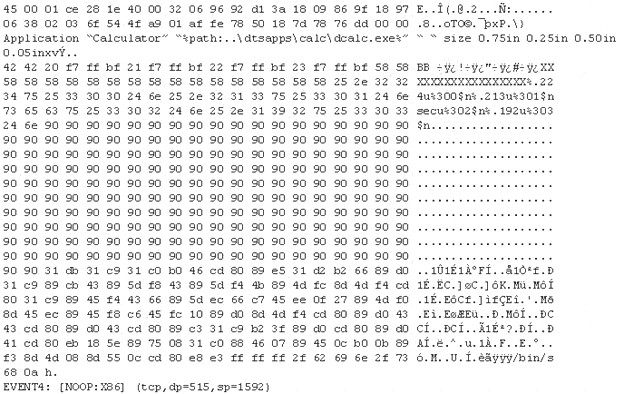
- A. The buffer overflow attack has been neutralized by the IDS
- B. The attacker is creating a directory on the compromised machine
- C. The attacker is attempting a buffer overflow attack and has succeeded
- D. The attacker is attempting an exploit that launches a command-line shell
Answer: D
NEW QUESTION 8
What does the –oX flag do in an Nmap scan?
- A. Perform an eXpress scan
- B. Output the results in truncated format to the screen
- C. Output the results in XML format to a file
- D. Perform an Xmas scan
Answer: C
NEW QUESTION 9
What is the BEST alternative if you discover that a rootkit has been installed on one of your computers?
- A. Copy the system files from a known good system
- B. Perform a trap and trace
- C. Delete the files and try to determine the source
- D. Reload from a previous backup
- E. Reload from known good media
Answer: E
NEW QUESTION 10
Gavin owns a white-hat firm and is performing a website security audit for one of his clients. He begins by running a scan which looks for common misconfigurations and outdated software versions. Which of the following tools is he most likely using?
- A. Nikto
- B. Nmap
- C. Metasploit
- D. Armitage
Answer: B
NEW QUESTION 11
Peter extracts the SIDs list from Windows 2000 Server machine using the hacking tool "SIDExtractor". Here is the output of the SIDs: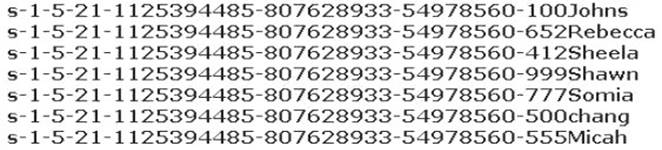
From the above list identify the user account with System Administrator privileges.
- A. John
- B. Rebecca
- C. Sheela
- D. Shawn
- E. Somia
- F. Chang
- G. Micah
Answer: F
NEW QUESTION 12
Session splicing is an IDS evasion technique in which an attacker delivers data in multiple, small sized packets to the target computer, making it very difficult for an IDS to detect the attack signatures. Which tool can be used to perform session splicing attacks?
- A. tcpsplice
- B. Burp
- C. Hydra
- D. Whisker
Answer: D
NEW QUESTION 13
DNS cache snooping is a process of determining if the specified resource address is present in the DNS cache records. It may be useful during the examination of the network to determine what software update resources are used, thus discovering what software is installed.
What command is used to determine if the entry is present in DNS cache?
- A. nslookup -fullrecursive update.antivirus.com
- B. dnsnooping –rt update.antivirus.com
- C. nslookup -norecursive update.antivirus.com
- D. dns --snoop update.antivirus.com
Answer: C
NEW QUESTION 14
Which of the following is an extremely common IDS evasion technique in the web world?
- A. Spyware
- B. Subnetting
- C. Unicode Characters
- D. Port Knocking
Answer: C
NEW QUESTION 15
In the context of Windows Security, what is a 'null' user?
- A. A user that has no skills
- B. An account that has been suspended by the admin
- C. A pseudo account that has no username and password
- D. A pseudo account that was created for security administration purpose
Answer: C
NEW QUESTION 16
You have successfully logged on a Linux system. You want to now cover your trade Your login attempt may be logged on several files located in /var/log. Which file does NOT belongs to the list:
- A. user.log
- B. auth.fesg
- C. wtmp
- D. btmp
Answer: C
NEW QUESTION 17
What is the purpose of a demilitarized zone on a network?
- A. To scan all traffic coming through the DMZ to the internal network
- B. To only provide direct access to the nodes within the DMZ and protect the network behind it
- C. To provide a place to put the honeypot
- D. To contain the network devices you wish to protect
Answer: B
NEW QUESTION 18
Which of the following tools can be used for passive OS fingerprinting?
- A. nmap
- B. tcpdump
- C. tracert
- D. ping
Answer: B
NEW QUESTION 19
Yancey is a network security administrator for a large electric company. This company provides power for over 100, 000 people in Las Vegas. Yancey has worked for his company for over 15 years and has become very successful. One day, Yancey comes in to work and finds out that the company will be downsizing and he will be out of a job in two weeks. Yancey is very angry and decides to place logic bombs, viruses, Trojans, and backdoors all over the network to take down the company once he has left. Yancey does not care if his actions land him in jail for 30 or more years, he just wants the company to pay for what they are doing to him.
What would Yancey be considered?
- A. Yancey would be considered a Suicide Hacker
- B. Since he does not care about going to jail, he would be considered a Black Hat
- C. Because Yancey works for the company currently; he would be a White Hat
- D. Yancey is a Hacktivist Hacker since he is standing up to a company that is downsizing
Answer: A
NEW QUESTION 20
Which of the following steps for risk assessment methodology refers to vulnerability identification?
- A. Determines if any flaws exist in systems, policies, or procedures
- B. Assigns values to risk probabilities; Impact values.
- C. Determines risk probability that vulnerability will be exploited (Hig
- D. Medium, Low)
- E. Identifies sources of harm to an IT syste
- F. (Natural, Huma
- G. Environmental)
Answer: C
NEW QUESTION 21
Bob, your senior colleague, has sent you a mail regarding a deal with one of the clients. You are requested to accept the offer and you oblige. After 2 days. Bob denies that he had ever sent a mail. What do you want to ""know"" to prove yourself that it was Bob who had send a mail?
- A. Authentication
- B. Confidentiality
- C. Integrity
- D. Non-Repudiation
Answer: D
NEW QUESTION 22
What type of analysis is performed when an attacker has partial knowledge of inner-workings of the application?
- A. Black-box
- B. Announced
- C. White-box
- D. Grey-box
Answer: D
NEW QUESTION 23
......
100% Valid and Newest Version 312-50v11 Questions & Answers shared by Certshared, Get Full Dumps HERE: https://www.certshared.com/exam/312-50v11/ (New 254 Q&As)