350-701 | How Many Questions Of 350-701 Exam Question
Best Quality of 350-701 free draindumps materials and test question for Cisco certification for candidates, Real Success Guaranteed with Updated 350-701 pdf dumps vce Materials. 100% PASS Implementing and Operating Cisco Security Core Technologies exam Today!
Free 350-701 Demo Online For Cisco Certifitcation:
NEW QUESTION 1
When wired 802.1X authentication is implemented, which two components are required? (Choose two.)
- A. authentication server: Cisco Identity Service Engine
- B. supplicant: Cisco AnyConnect ISE Posture module
- C. authenticator: Cisco Catalyst switch
- D. authenticator: Cisco Identity Services Engine
- E. authentication server: Cisco Prime Infrastructure
Answer: AC
Explanation:
Reference: https://www.lookingpoint.com/blog/ise-series-802.1x
NEW QUESTION 2
An MDM provides which two advantages to an organization with regards to device management? (Choose two.)
- A. asset inventory management
- B. allowed application management
- C. Active Directory group policy management
- D. network device management
- E. critical device management
Answer: AB
NEW QUESTION 3
An engineer is configuring AMP for endpoints and wants to block certain files from executing. Which outbreak control method is used to accomplish this task?
- A. device flow correlation
- B. simple detections
- C. application blocking list
- D. advanced custom detections
Answer: C
NEW QUESTION 4
An engineer needs a solution for TACACS+ authentication and authorization for device administration. The engineer also wants to enhance wired and wireless network security by requiring users and endpoints to use 802.1X, MAB, or WebAuth. Which product meets all of these requirements?
- A. Cisco Prime Infrastructure
- B. Cisco Identity Services Engine
- C. Cisco Stealthwatch
- D. Cisco AMP for Endpoints
Answer: B
NEW QUESTION 5
In which form of attack is alternate encoding, such as hexadecimal representation, most often observed?
- A. smurf
- B. distributed denial of service
- C. cross-site scripting
- D. rootkit exploit
Answer: C
NEW QUESTION 6
An administrator wants to ensure that all endpoints are compliant before users are allowed access on the corporate network. The endpoints must have the corporate antivirus application installed and be running the latest build of Windows 10. What must the administrator implement to ensure that all devices are compliant before they are allowed on the network?
- A. Cisco Identity Services Engine and AnyConnect Posture module
- B. Cisco Stealthwatch and Cisco Identity Services Engine integration
- C. Cisco ASA firewall with Dynamic Access Policies configured
- D. Cisco Identity Services Engine with PxGrid services enabled
Answer: A
Explanation:
Reference: https://www.cisco.com/c/en/us/td/docs/security/vpn_client/anyconnect/anyconnect46/administration/guide/b_AnyConnect_Administrator_Guide_4-6/configure-posture.html
NEW QUESTION 7
Which Cisco solution does Cisco Umbrella integrate with to determine if a URL is malicious?
- A. AMP
- B. AnyConnect
- C. DynDNS
- D. Talos
Answer: D
NEW QUESTION 8
Which policy is used to capture host information on the Cisco Firepower Next Generation Intrusion Prevention System?
- A. correlation
- B. intrusion
- C. access control
- D. network discovery
Answer: D
NEW QUESTION 9
The Cisco ASA must support TLS proxy for encrypted Cisco Unified Communications traffic. Where must the ASA be added on the Cisco UC Manager platform?
- A. Certificate Trust List
- B. Endpoint Trust List
- C. Enterprise Proxy Service
- D. Secured Collaboration Proxy
Answer: A
Explanation:
Reference: https://www.cisco.com/c/en/us/td/docs/security/asa/special/unified-communications/guide/unified-comm/unified-comm-tlsproxy.html
NEW QUESTION 10
In which cloud services model is the tenant responsible for virtual machine OS patching?
- A. IaaS
- B. UCaaS
- C. PaaS
- D. SaaS
Answer: A
Explanation:
Reference: https://www.cmswire.com/cms/information-management/cloud-service-models-iaas-saas-paas-how-microsoft-office-365-azure-fit-in-021672.php
NEW QUESTION 11
An engineer is configuring a Cisco ESA and wants to control whether to accept or reject email messages to a recipient address. Which list contains the allowed recipient addresses?
- A. SAT
- B. BAT
- C. HAT
- D. RAT
Answer: D
NEW QUESTION 12
Which two capabilities does TAXII support? (Choose two.)
- A. exchange
- B. pull messaging
- C. binding
- D. correlation
- E. mitigating
Answer: BC
NEW QUESTION 13
An engineer must force an endpoint to re-authenticate an already authenticated session without disrupting the endpoint to apply a new or updated policy from ISE. Which CoA type achieves this goal?
- A. Port Bounce
- B. CoA Terminate
- C. CoA Reauth
- D. CoA Session Query
Answer: C
NEW QUESTION 14
How is Cisco Umbrella configured to log only security events?
- A. per policy
- B. in the Reporting settings
- C. in the Security Settings section
- D. per network in the Deployments section
Answer: A
Explanation:
Reference: https://docs.umbrella.com/deployment-umbrella/docs/log-management
NEW QUESTION 15
What can be integrated with Cisco Threat Intelligence Director to provide information about security threats, which allows the SOC to proactively automate responses to those threats?
- A. Cisco Umbrella
- B. External Threat Feeds
- C. Cisco Threat Grid
- D. Cisco Stealthwatch
Answer: C
NEW QUESTION 16
Refer to the exhibit.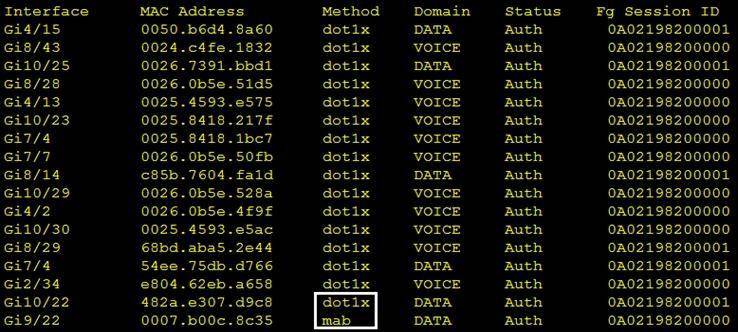
Which command was used to generate this output and to show which ports are authenticating with dot1x or mab?
- A. show authentication registrations
- B. show authentication method
- C. show dot1x all
- D. show authentication sessions
Answer: B
NEW QUESTION 17
......
P.S. Easily pass 350-701 Exam with 337 Q&As Dumps-hub.com Dumps & pdf Version, Welcome to Download the Newest Dumps-hub.com 350-701 Dumps: https://www.dumps-hub.com/350-701-dumps.html (337 New Questions)